What is Nextcloud?
TLDR: A Nextcloud description is below, but why not just check out the demo!
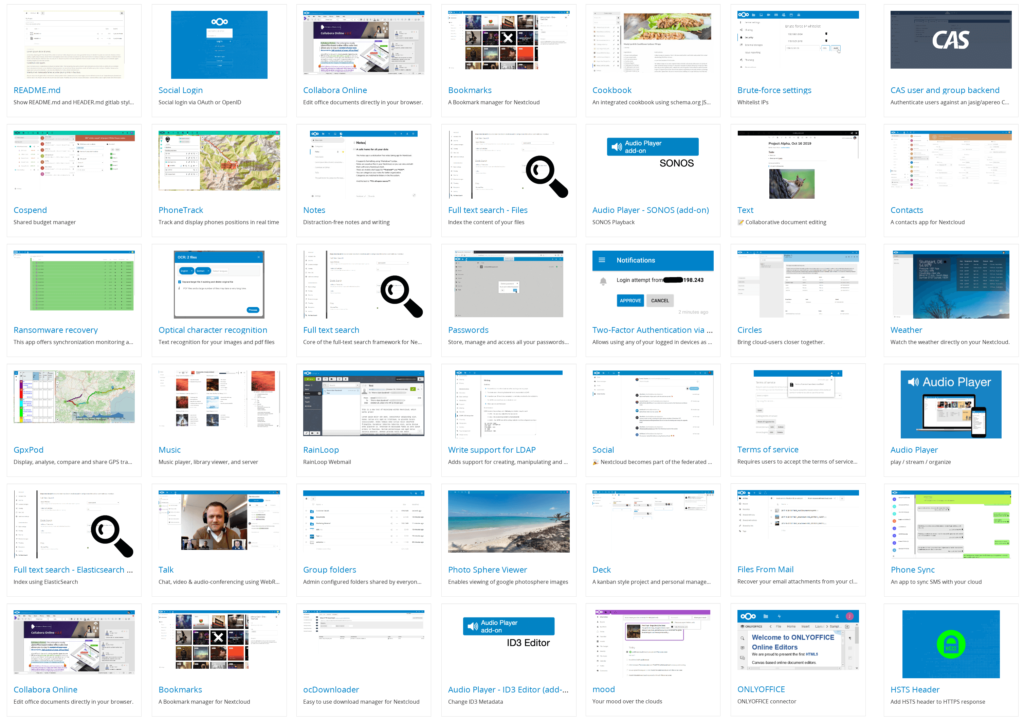
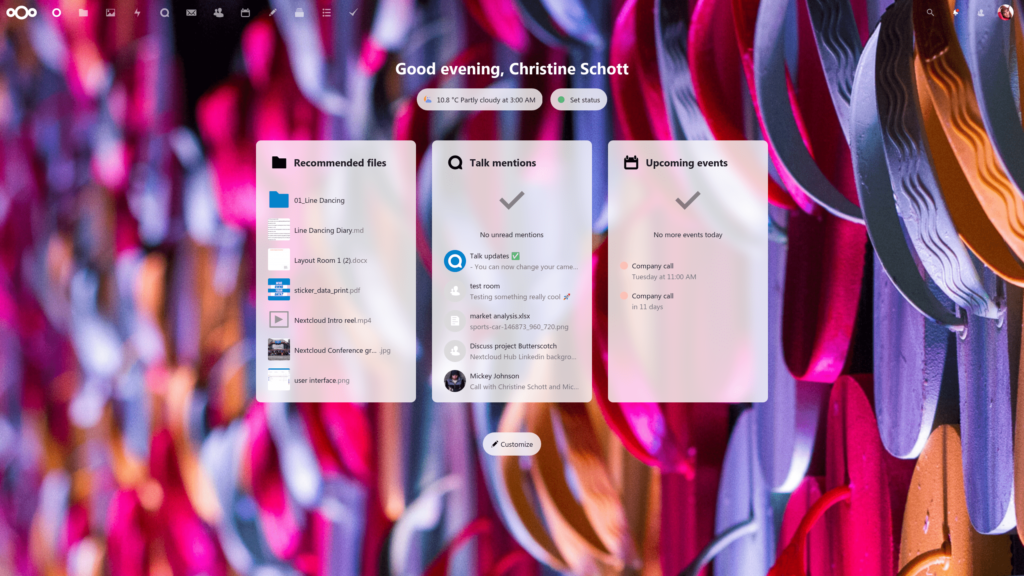
Nextcloud is a Free and Open Source Software (FOSS) that provides an enterprise grade all-in-one solution for file storage, collaboration, meetings, etc. Over the past few years Nextcloud has come a long way and is now my recommended solution for anyone seriously interested in hosting their own data with privacy and security in mind. Nextcloud is made up of many, many apps that can be installed as needed. Some of the apps include:
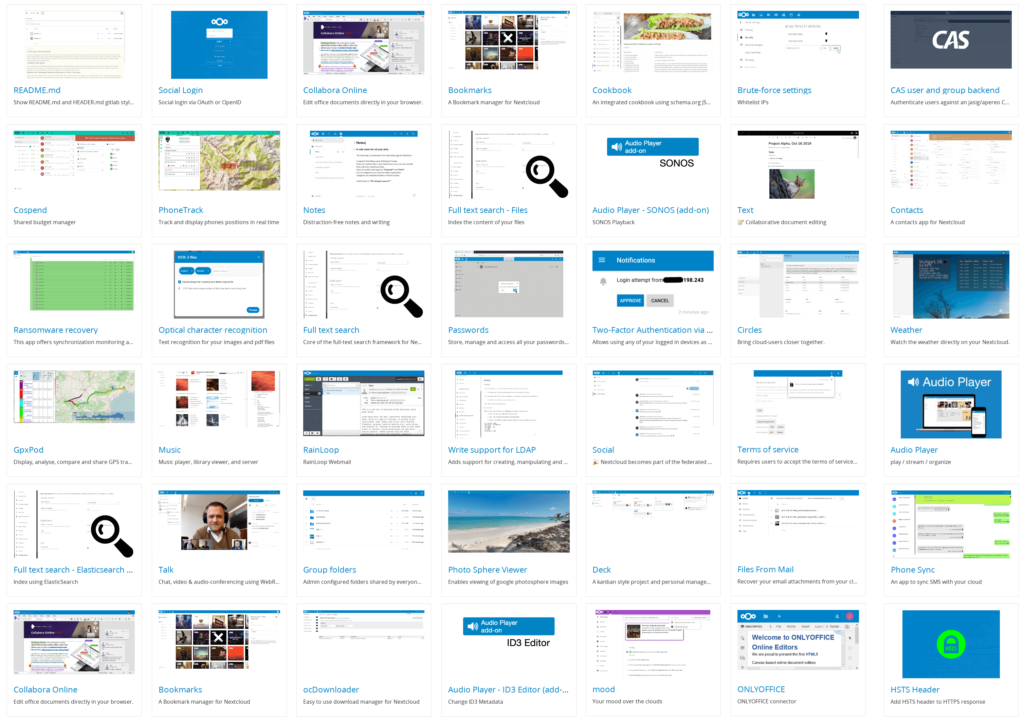
- Files (This is installed by default and aids in storing/sharing/managing your files)
- Calendar (This uses WebDav and can be synced to other devices more on this in a later post)
- Tasks (This also can be synced using WebDav to other devices like MacOS/iOS Reminders)
- Gallery (This helps with managing your photos in a centralized location)
- Maps (Directions, pinning locations, mapping where your photos were taken, etc)
- Contacts (Address book that uses WebDav to sync with other devices)
- Bookmarks (Bookmark storage that can be synced to your browser using Floccus)
- Talk (Meeting software like Zoom or Jitsi, no Nextcloud account needed to join calls!)
- Mail (A very functional Mail client application with encryption, multiple accounts, etc)
- Other features:
- 2 Factor Authentication
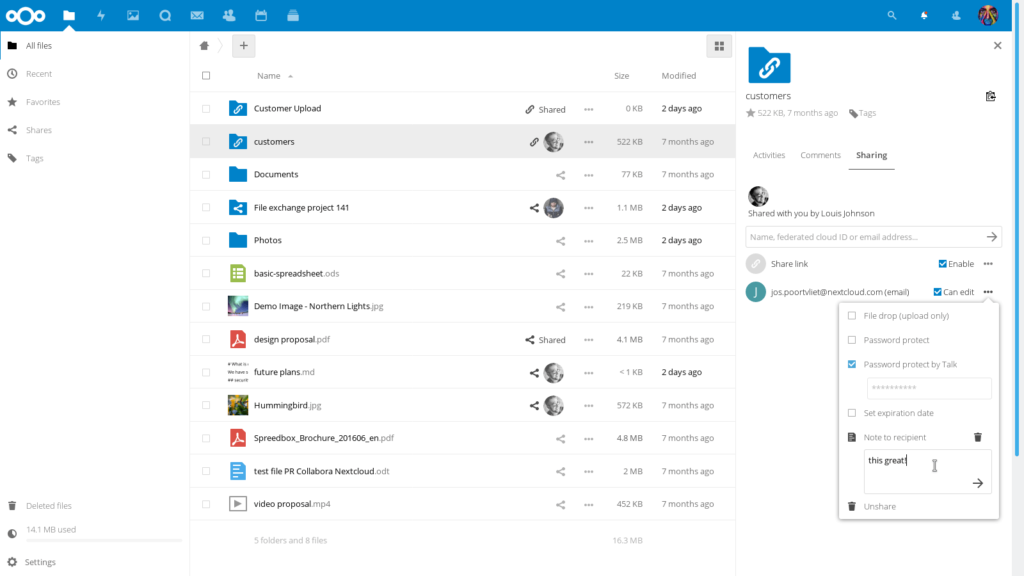
- File Sharing policies (timeframe, encryption options, public link expiration, etc)
- LDAP user/group managment
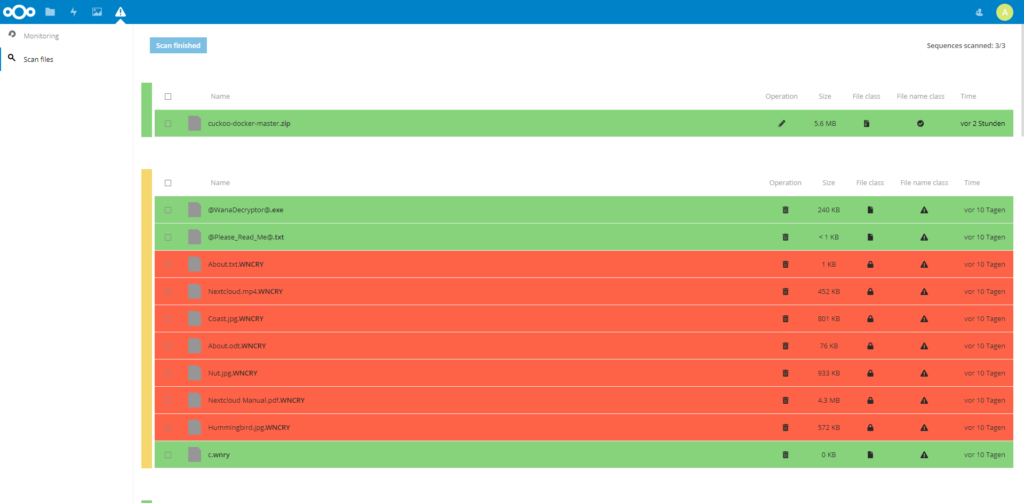
- Automated updates & Security audits
- Forms
- Polls
- Project Management
- Social Plugins
- Password Manager
- Many others (See the Nextcloud App Store)
Why Nextcloud?
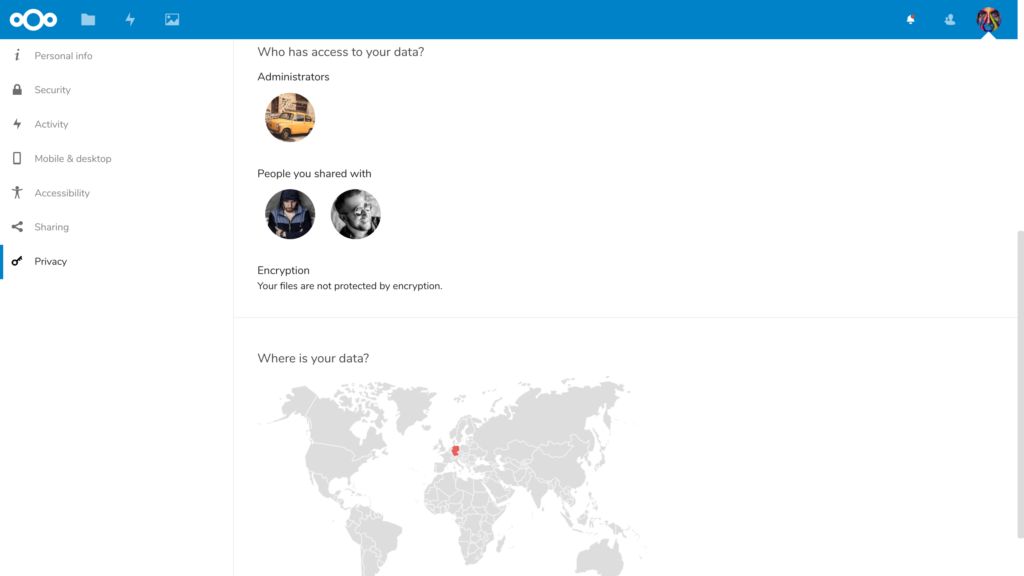
Why use Nextcloud? Simply put: data privacy. Nextcloud provides a private and secure vault for all your personal information. No need to worry about Google reading your emails and using your photos for machine learning purposes. No need to pay Dropbox or any other cloud storage company a monthly fee for storing your files on a server you have no control over. Nextcloud makes it easier to take responsibility for your own data so you know where it resides. If you’re still not convinced, check out Nextcloud’s reasoning.
When Nextcloud
Given my bullish stance on Nextcloud, I would also like to make clear that Nextcloud isn’t for everyone. It does require some technical experience and a use case that is worth while. Nextcloud works best and is most enjoyable when it is used for more than just a few files. Casual or non-technical Nextcloud users would be better off signing up with a Nextcloud provider rather then self-hosting it since the providers will handle the configuration and hosting of the storage (this however does reduce your visibility in where and how your data is stored). An alternative to a cloud provider is to buy a dedicated, pre-configured piece of Nextcloud hardware with some tech support.

How Nextcloud
Requirements
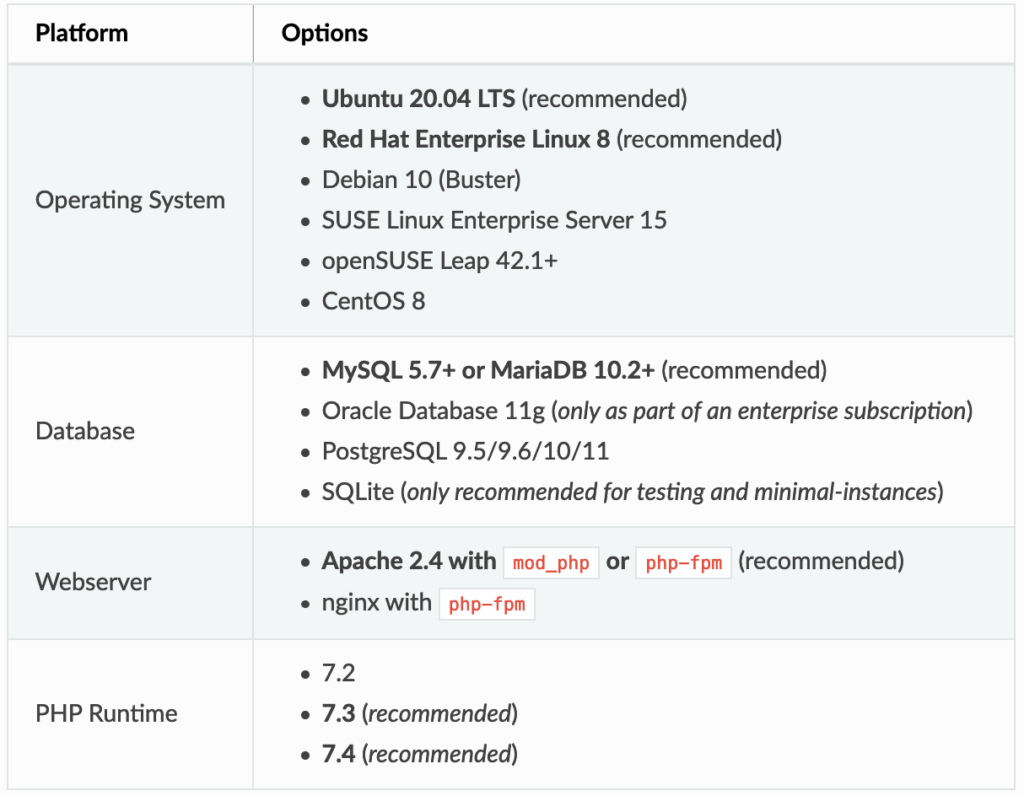
Nextcloud can be installed in a variety of ways. My preferred method is using the per-configured virtual appliance, but other methods include docker, Ubuntu snap, web-server script, archive extraction. Detailed installation instructions can be found in the Nextcloud Docs, but a simple rundown of the installation methods are listed below:
Appliance

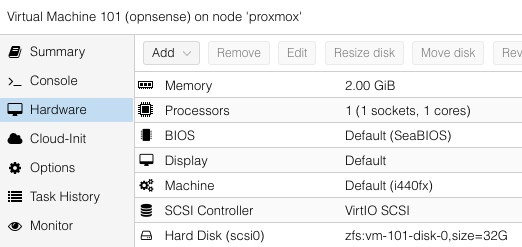
Virtual Machine (My preferred method)
I prefer this method since it allows me to take easy snapshots/backups of the entire Nextcloud environment. This gives me peace of mind so I can be sure I can rollback to a point in time if anything goes wrong.
- Download the Virtual Machine (There are also advanced-configured VMs here)
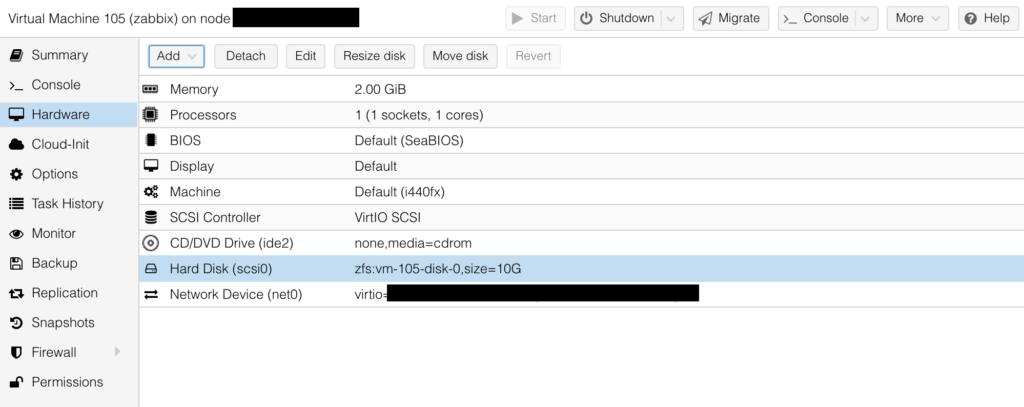
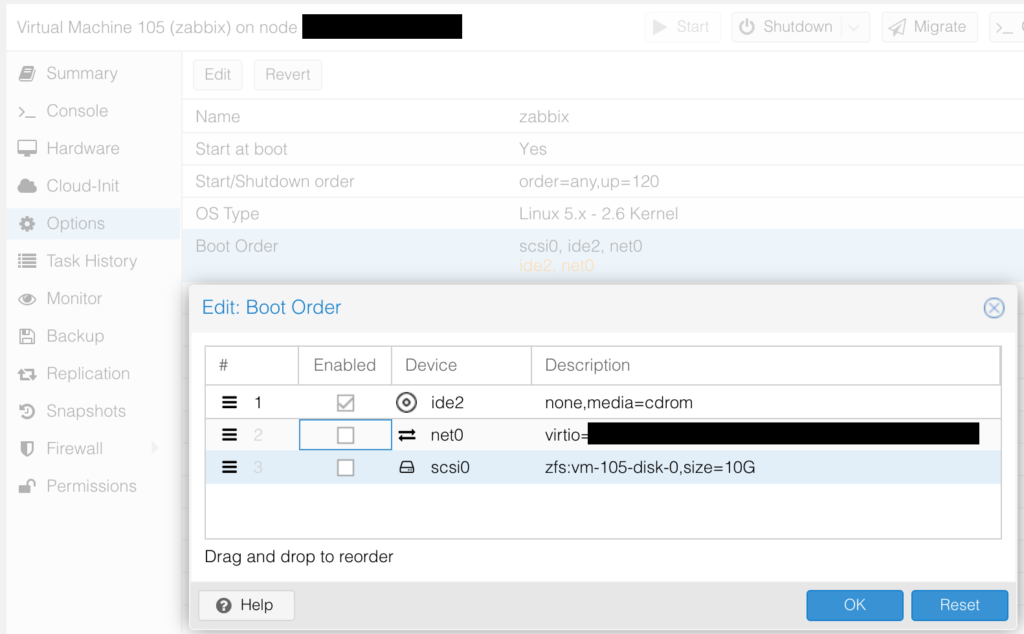
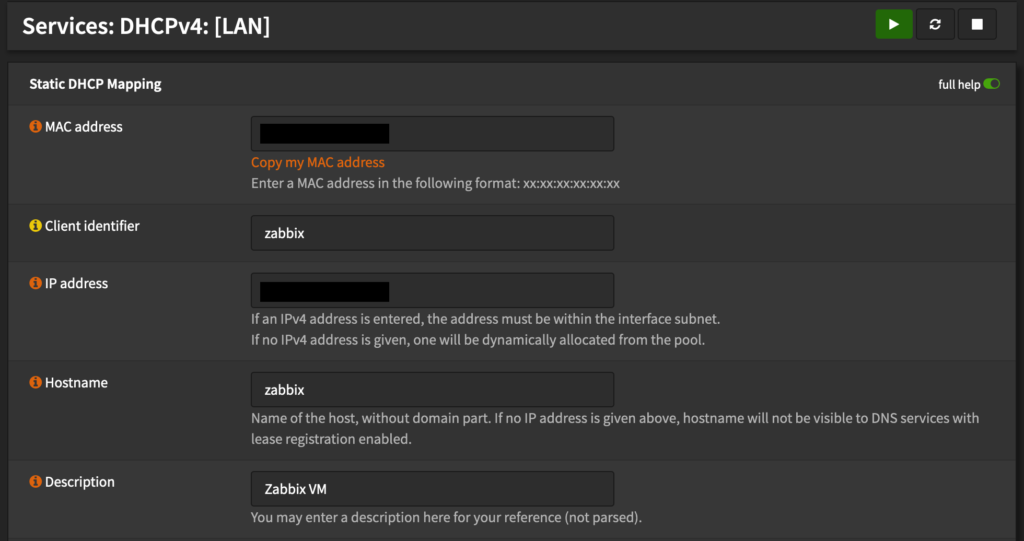
- Setup a VM in your favorite Hypervisor (Proxmox, Hyper-V, VirtualBox, VMWare, etc)
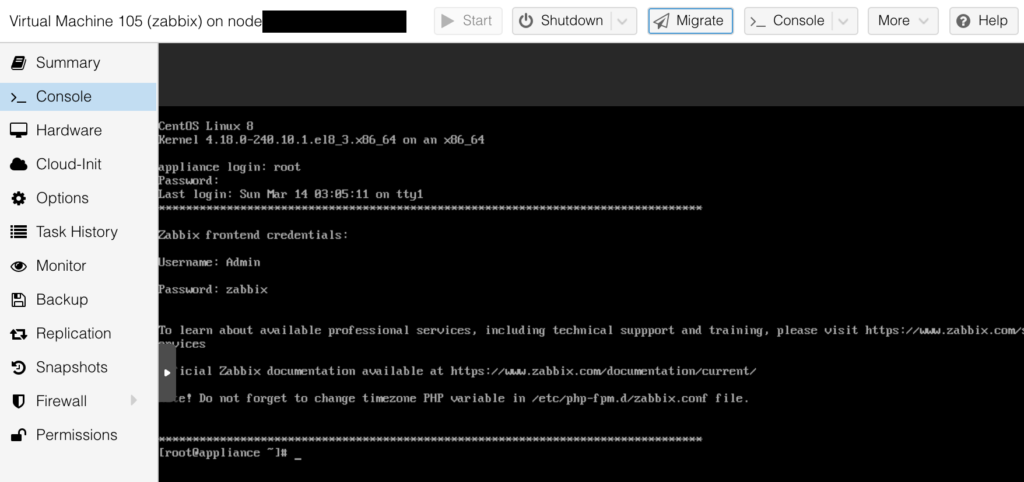
- Import the downloaded Virtual Machine file and start the virtual machine (check the console)
- Login to the pre-configured Nextcloud instance and enjoy!

Appliance: Docker (Great for those already using Docker)
For those already using docker, this method may be appealing. I avoided this option primarily because it didn’t have a very clean docker-compose setup.
- On a docker-enabled machine run `
docker run -d -p 8080:80 nextcloud` - Alternatively, if you use docker-compose, start with this template:
version: '2'
volumes:
nextcloud:
db:
services:
db:
image: mariadb
restart: always
command: --transaction-isolation=READ-COMMITTED --binlog-format=ROW
volumes:
- db:/var/lib/mysql
environment:
- MYSQL_ROOT_PASSWORD=
- MYSQL_PASSWORD=
- MYSQL_DATABASE=nextcloud
- MYSQL_USER=nextcloud
app:
image: nextcloud
restart: always
ports:
- 8080:80
links:
- db
volumes:
- nextcloud:/var/www/html
environment:
- MYSQL_PASSWORD=
- MYSQL_DATABASE=nextcloud
- MYSQL_USER=nextcloud
- MYSQL_HOST=db
Appliance: Ubuntu Snap (Easy for Beginners, but not recommended!)
This installation method is very easy but does have some drawbacks. From my experience, updates are slower to be released to the Nextcloud ubuntu snap distribution and often has issues with edge cases (I’ve noticed this with Collabora docs). It is also very difficult to migrate Nextcloud from a snap installation to a different installation method (I learned this the hard way!).
- Setup an ubuntu machine with snap enabled.
- Run `
snap install nextcloud` - Follow the installation steps and enjoy.

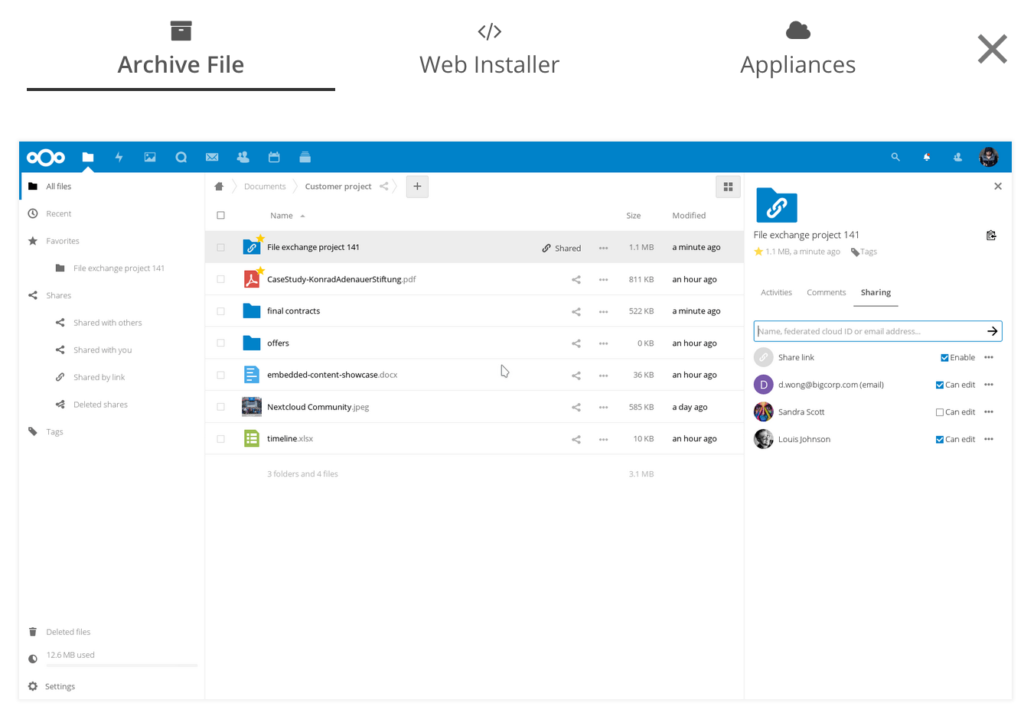
Web Installer (Good for C-Panel style web-hosting)
- Download the php script from the Nextcloud Site
- Upload the php scrip to your web server
- Point your browser to the php script
- Walk through the installation wizard (default user: ncadmin default password: nextcloud)
- Enjoy!
Manual Archive File Installation (Most Difficult)
- Download the Archive from the Nextcloud site
- Extract the archive file to an accessible location on your web server
- Configure Apache webserver
- Configure SSL
- Walk through installation wizard
Enjoy Nextcloud!
‘Don’t be Evil’ Isn’t enough for me!